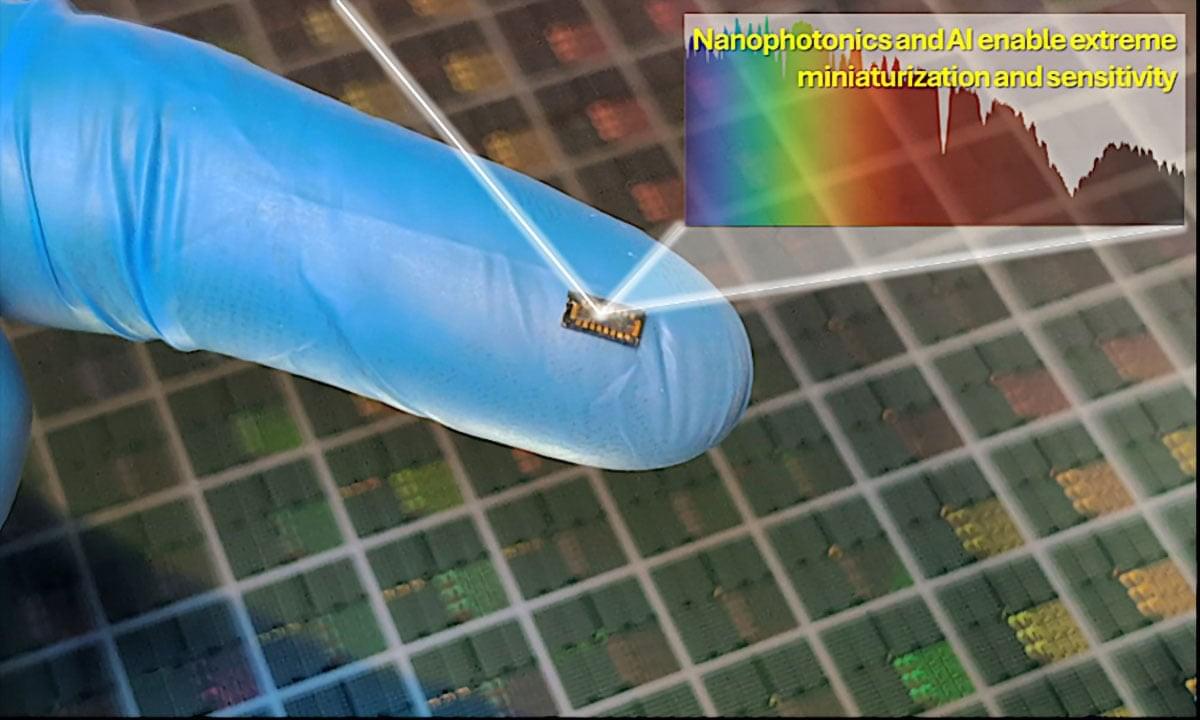
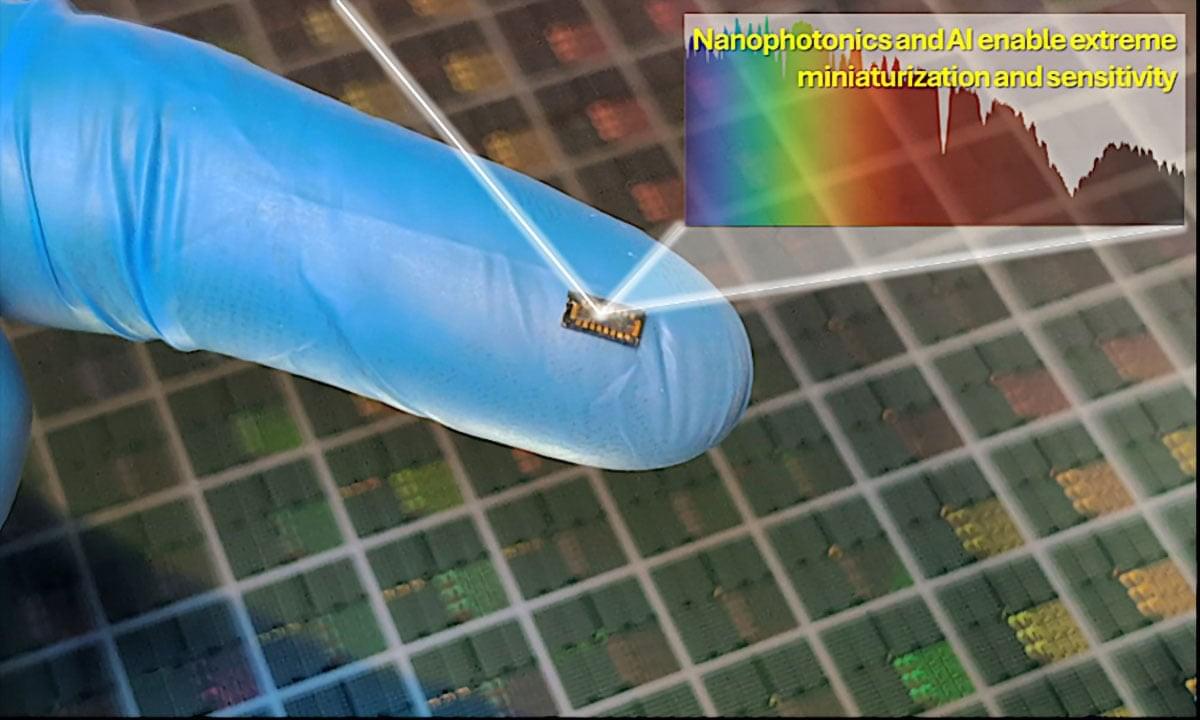
A new chip-scale spectrometer challenges the long-standing reliance on bulky optical systems by replacing physical light separation with computational reconstruction.




Cybersecurity researchers have discovered a new campaign in which a cluster of 108 Google Chrome extensions has been found to communicate with the same command-and-control (C2) infrastructure with the goal of collecting user data and enabling browser-level abuse by injecting ads and arbitrary JavaScript code into every web page visited.
According to Socket, the extensions (complete list here) are published under five distinct publisher identities – Yana Project, GameGen, SideGames, Rodeo Games, and InterAlt – and have collectively amassed about 20,000 installs in the Chrome Web Store.
“All 108 route stolen credentials, user identities, and browsing data to servers controlled by the same operator,” security researcher Kush Pandya said in an analysis.