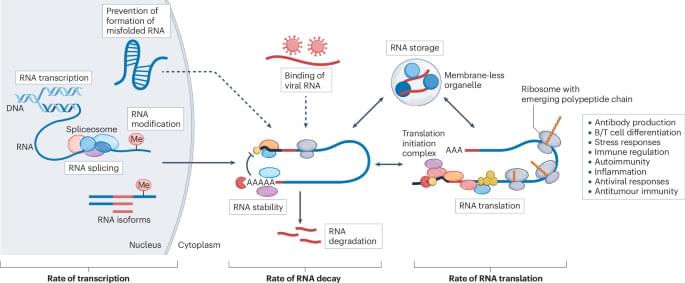
RNA-binding proteins (RBPs) considerably expand the information content of the genome and can determine the lifespan, localization and function of RNA, thereby controlling when, where and how much protein is produced. There is a growing body of evidence that links RBPs to specialized functions of immune cells and they can also mediate cell-autonomous immunity to foreign RNA and to misfolded self-RNAs. This Review examines how RBPs regulate the biogenesis and fate of mRNAs to mediate immune cell function and cell-autonomous immunity and their roles in immunodeficiency, autoimmunity and chronic inflammation.