A burgeoning field is launching its first clinical trial to find out whether dialling back cell development can safely refresh aged tissues and organs.


Neuron.
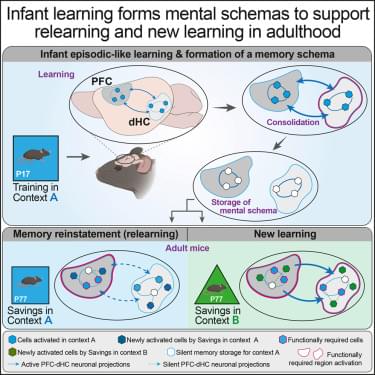
Bessières, Prikas, et al. report that episodic-like learning in infant mice establishes enduring memory schemas that guide adult behavior. The schema facilitates relearning and the formation of new, congruent memories in adulthood. Infantile schemas undergo hippocampus-dependent systems consolidation. While adult relearning relies on the PFC, the facilitation of new congruent memories requires PFC and top-down PFC-to-hippocampus neural projections.
You just haven’t noticed.
George Church, Harvard geneticist and Human Genome Project pioneer, explains why CRISPR wasn’t the real breakthrough, how multiplex gene editing unlocked organ transplants and de-extinction, and why aging will likely require rewriting many genes at once.
Hosted by Mgoes → https://twitter.com/m_goes_distance
Brought to you by SuperHuman Fund → https://superhuman.fund/
0:00 — Gene Editing Mammals → Humans
8:36 — Germline vs Somatic
14:56 — Modified Humans Are Already Here
18:50 — Enhancing Healthy Humans
25:00 — Aging Therapies vs Cognitive Enhancement
30:20 — Embryo Selection
38:10 — Is US Losing To UAE?
42:33 — Biotech Failures
49:31 — Next Dire Wolf Moment
54:21 — AI x Science
1:02:07 — Synthetizing Entire Genomes.
The Accelerate Bio Podcast explores the future of humanity in the age of Artificial Intelligence. Subscribe for deep-dive conversations with founders, scientists, and investors shaping AI, biotechnology, and human progress.
This episode discusses George Church, gene editing, CRISPR, human enhancement, longevity, aging, embryo selection, synthetic biology, multiplex editing, AI biotech.
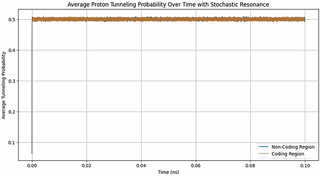
Time may be viewed as an emergent consequence of increasing information entropy. I explore a toy quantum‑information model in which DNA is treated as an open quantum system. In this framework, weak, time‑dependent perturbations (potentially arising from thermal fluctuations, ionic microfields, metabolic noise, or electromagnetic signals) bias the micro‑timing of events during replication and repair. These slight timing shifts can influence the fate of transient electronic and protonic configurations (including short‑lived tautomeric states driven by proton‑transfer tunnelling), subtly altering mutation probabilities. To test this idea, I map nucleotides in the Mycobacterium tuberculosis genome to constrained qubit states and quantify informational structure using Shannon and von Neumann entropies and coding to non‑coding correlation metrics. Simulations of Hamiltonian dynamics under physiologically plausible perturbations show that real genomic segments exhibit distinctive dynamical signatures compared with controls. I also examine a variant in which a weak, slowly varying external signal is introduced as a background “beat” against which DNA dynamics can be compared. Because a Doppler shift in electromagnetic waves encodes the flow of time through the relative motion of source and observer, a cosmic microwave background (CMB) with a tiny frequency drift provides a conceptual clock and a source of informational entropy: it feeds a time‑correlated input into the DNA quantum system, allowing the molecule to sample cosmic time and translate it into a biological scale by modulating tunnelling probabilities and thus mutation patterns. This CMB‑inspired drive is simply a convenient illustration; the model does not rely on it, and other sources of weakly structured entropy could be tested. Across simulations, sequence‑dependent responses to both intrinsic and structured perturbations generate testable predictions: changing the structure or timing of these weak perturbations should produce reproducible shifts in mutation spectra. This framework connects cellular ageing and evolution to the flow of cosmic time and suggests experiments to probe DNA’s sensitivity to time‑dependent perturbations.
Citation: Garcia NA (2026) DNA as a quantum system in evolution. PLoS One 21: e0344520. https://doi.org/10.1371/journal.pone.
Editor: Yang Jack Lu, Beijing Technology and Business University, CHINA.

Though the point of a blog post like this is to get eyes on its event, it doesn’t just seem like lip service. Framework has been making modular laptops for years now, and even put out a desktop last year. Last year, the Framework 12 laptop got a 10/10 from iFixit regarding its repairability.
Framework says that every product it ships is in service of making computers “you can own at the deepest level and do what you want with.”
Framework, like almost every company, has been hit by the memory crisis. In January this year, it reportedly “held off as long as we could” but had to jack up the prices of its desktops and mainboards. And just this week, Framework said stabilising memory prices are simply a ‘temporary reprieve’ and that there would be more price increases to come in 2026.

The trillions of microbes living in the human gut are increasingly recognized as important partners in human health. Scientists have linked the gut microbiome to several aspects of health, from metabolism and immunity to mental health.
A recent study suggests that these microbes may also influence an important aspect of fitness—muscle strength.
Muscle strength is a crucial feature of health for many reasons. It supports our joints and keeps our bones healthy, boosts athletic performance and even plays a role in metabolic health.

A scorching “lava world” once thought barren may actually be wrapped in a thick, mysterious atmosphere. Astronomers have uncovered surprising evidence of a thick atmosphere surrounding TOI-561 b, a scorching, fast-orbiting rocky planet once thought too extreme to hold onto any gas. Using NASA’s James Webb Space Telescope, researchers found the planet is far cooler than expected for a bare rock, hinting at a heat-distributing atmosphere above a churning magma ocean. This strange world—where a year lasts just over 10 hours and one side is locked in eternal daylight—may even be rich in volatile materials, behaving like a “wet lava ball.”
A team of astronomers led by Carnegie has uncovered the clearest evidence yet that a rocky planet outside our Solar System has an atmosphere. Using NASA’s James Webb Space Telescope (JWST), the researchers identified signs of gas surrounding an unusual target: an ancient, extremely hot super Earth that likely has a surface covered by molten rock. The findings were published in The Astrophysical Journal Letters.
The planet, known as TOI-561 b, has about twice the mass of Earth but is dramatically different in almost every other way. It orbits extremely close to its star, at a distance just one fortieth that of Mercury from the Sun. Even though its star is slightly smaller and cooler than our Sun, the planet’s tight orbit means it completes a full year in only 10.56 hours. One side constantly faces the star, leaving it locked in permanent daylight.
This week, Laurie Segall sits down exclusively with OpenAI CEO Sam Altman for his first interview since shutting down the Disney-partnered Sora and making the Department of War deal. From power to parenthood, tech addiction and AI acceleration, Laurie interviews Altman about AI’s human impact and the weight of OpenAI’s influence. In a wide ranging interview, Altman describes a near-term future where automated AI researchers could compress a decade of scientific discovery into a single year, fundamentally reshaping society and an era of AI abundance, where solo-founders can build billion-dollar companies with AI agents. But that innovation sits against a complex backdrop with fundamental human questions at stake. Altman addresses concerns over AI-related job loss and reveals what he thinks are AI-proof jobs. Altman, who is also a father, discusses parenting in the age of AI, when he plans to introduce his own product to his child, and how he believes AI could benefit kids in the long run. This is a conversation with Sam Altman you’re not going to hear anywhere else, where the tech titan answers some fundamental questions about control, innovation, consequences, and the world we’ll leave behind for our children.
If you have thoughts or questions for Laurie about this episode or anything Mostly Human, email us at [email protected]