ComicForm phishing since April 2025 targets Belarus, Kazakhstan, Russia using Formbook malware, evading Microsoft Defender.


A vulnerability in the American Archive of Public Broadcasting’s website allowed downloading of protected and private media for years, with the flaw quietly patched this month.
BleepingComputer was tipped about the flaw by a cybersecurity researcher who asked to remain anonymous, stating that the flaw has been exploited since at least 2021, even after the researcher previously reported it to the organization.
After contacting AAPB about the flaw, a spokesperson confirmed the issue, and the researcher validated that the fix was implemented within 48 hours.
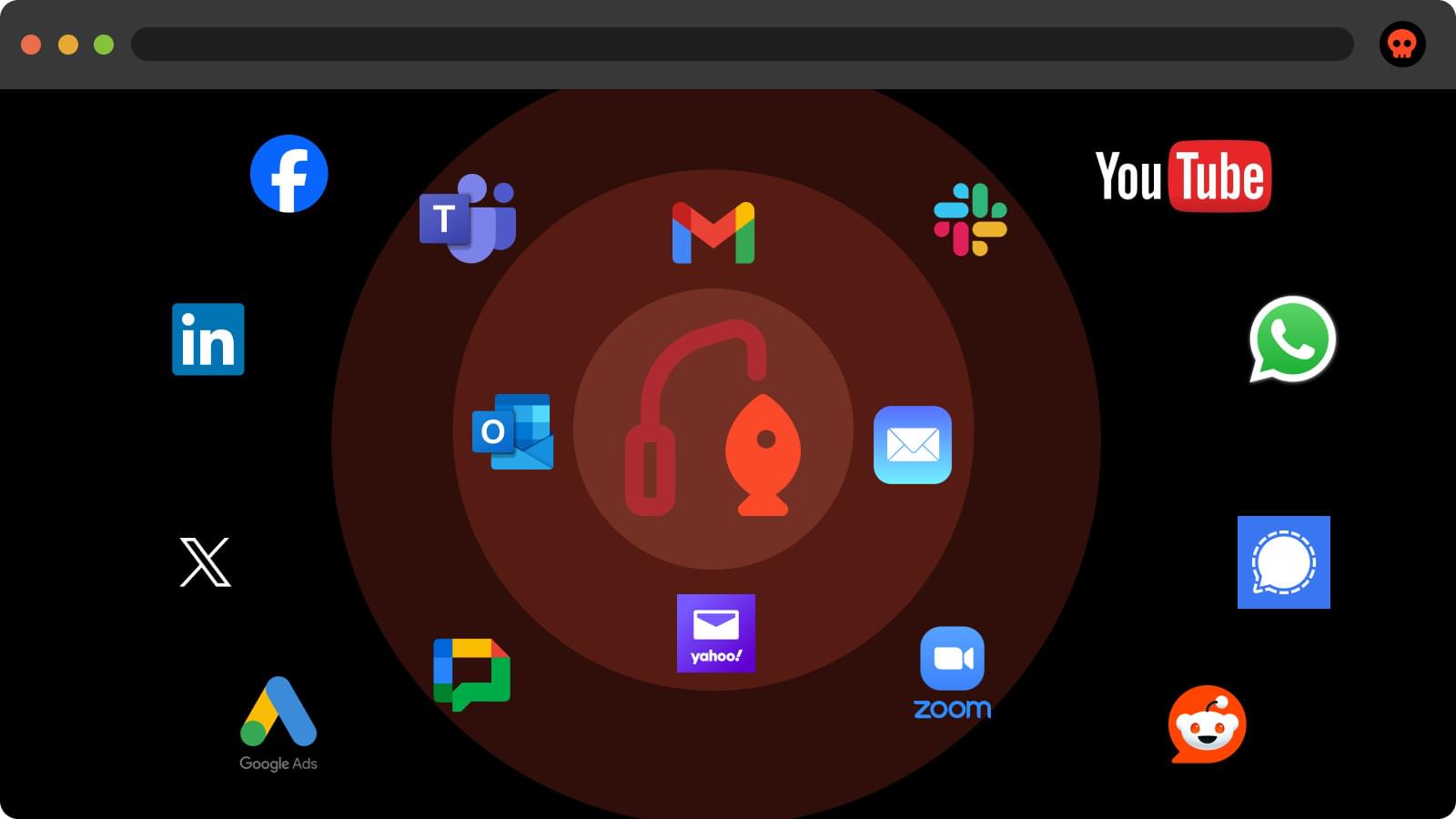




The phishing-as-a-service (PhaaS) offering known as Lighthouse and Lucid has been linked to more than 17,500 phishing domains targeting 316 brands from 74 countries.
“Phishing-as-a-Service (PhaaS) deployments have risen significantly recently,” Netcraft said in a new report. “The PhaaS operators charge a monthly fee for phishing software with pre-installed templates impersonating, in some cases, hundreds of brands from countries around the world.”
Lucid was first documented by Swiss cybersecurity company PRODAFT earlier this April, detailing the phishing kit’s ability to send smishing messages via Apple iMessage and Rich Communication Services (RCS) for Android.

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published an analysis of the malware deployed in attacks exploiting vulnerabilities affecting Ivanti Endpoint Manager Mobile (EPMM).
The flaws are an authentication bypass in EPMM’s API component (CVE-2025–4427) and a code injection vulnerability (CVE-2025–4428) that allows execution of arbitrary code.
The two vulnerabilities affect the following Ivanti EPMM development branches and their earlier releases: 11.12.0.4, 12.3.0.1, 12.4.0.1, and 12.5.0.0.

A team of scientists at Simon Fraser University’s Quantum Technology Lab and leading Canada-based quantum company Photonic Inc. have created a new type of silicon-based quantum device controlled both optically and electrically, marking the latest breakthrough in the global quantum computing race.
The research, published in the journal Nature Photonics, reveals new diode nanocavity devices for electrical control over silicon color center qubits.
The devices have achieved the first-ever demonstration of an electrically-injected single-photon source in silicon. The breakthrough clears another hurdle toward building a quantum computer—which has enormous potential to provide computing power well beyond that of today’s supercomputers and advance fields like chemistry, materials science, medicine and cybersecurity.
