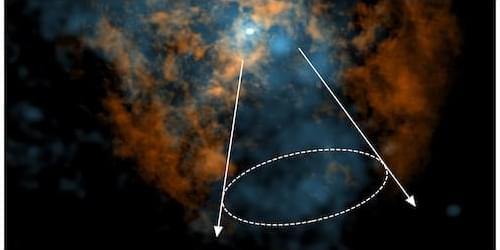
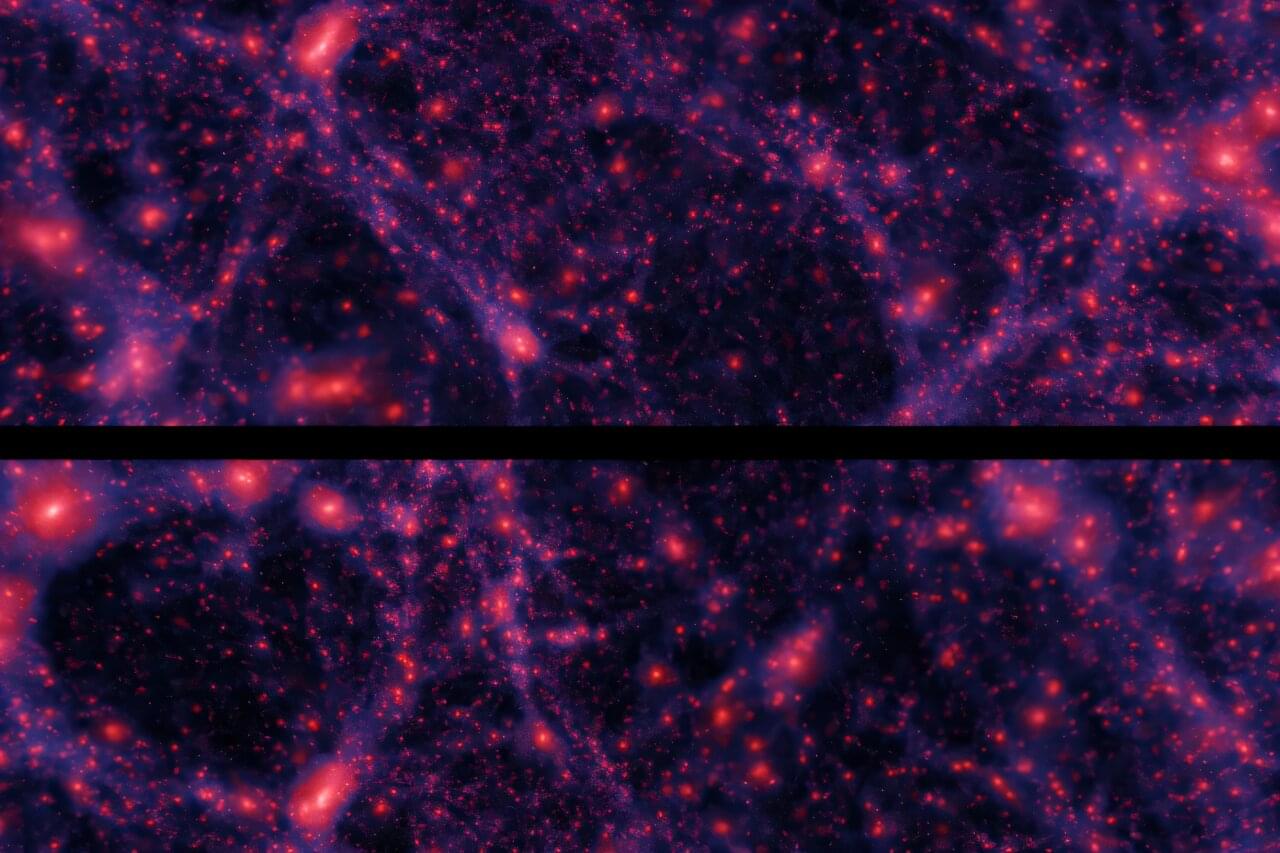
Astronomers may have solved a long-standing puzzle surrounding the giant black hole lurking at the center of our Galaxy, Sagittarius A* (Sgr A•. Using observations from the Atacama Large Millimeter/submillimeter Array (ALMA) radio observatory in Chile, Mark Gorski and Lena Murchikova of Northwestern University in Illinois have obtained signatures of a previously elusive wind from Sgr A* [1]. Such a wind had long been predicted but was never convincingly observed. If confirmed, the discovery could offer a rare glimpse into how the majority of supermassive black holes interact with their surroundings.
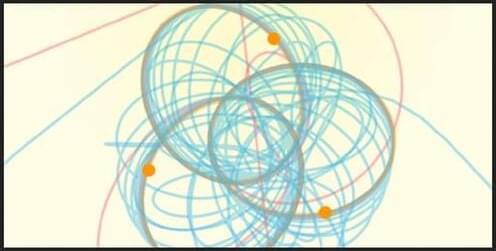
Supermassive black holes grow by accreting dust, stars, and gas in their vicinity. Nothing can escape the event horizon, but the turbulent environment outside of the horizon can propel gas outward in the form of jets and winds. Giant jets of plasma—such as the one emerging from M87*, the first black hole ever imaged—can be launched by twisted magnetic fields acting like cosmic slingshots. The same environment can drive less collimated outflows, or winds, through a combination of magnetic forces, thermal pressure, and radiation. Loosely speaking, “jets are to winds what laser pointers are to flashlights,” Gorski says.
Much of our understanding of these phenomena comes from the most extreme objects, such as quasars and active galactic nuclei, where winds and jets have been extensively documented. But most supermassive black holes, including Sgr A*, are thought to display less fireworks, living in quiescent, low-luminosity states that are far more difficult to study. Theory still predicts that these “quiet” black holes should fuel winds, but decades of observations of the closest black hole in the sky could not confirm such predictions. “The absence of a wind was one of the most uncomfortable things about our own Galaxy’s black hole,” Murchikova says.